(This overview of Business Continuity Management is a guest post by Dipali Inamdar, Head of IT Security in Geometric)
In emergency situations like pandemic outbreaks, power failures, riots, strikes, infrastructure issues, it is important that your business does not stop functioning. A plan to ensure this is called a Business Continuity Plan (BCP), and it is of prime importance to your business to ensure minimum disruption and smooth functioning of your operations. Earlier most companies would document business continuity plans only if their clients asked for it and would focus mainly on IT recovery. But scenarios have changed now. Corporations of all sized have now realized the importance of keeping their business functioning at all time and hence they are working towards a well defined business continuity management framework. Business continuity (BC) is often understood as a process to handle events that could disrupt business. However, BC is more than just recovery. The plan should also ensure proper business resumption after recovering from the disruption.
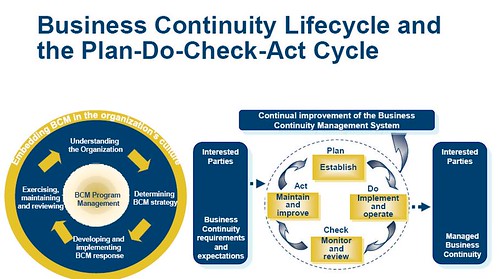
Business continuity management is a continuous life cycle as follows:
How does one start with BCM?
Business Impact Analysis (understanding the organization)
The first step is to conduct a Business Impact analysis. This would help you to identity critical business systems and processes and how their outage (downtime) could affect your business. You cannot have plan in place for all the processes without considering financial investments needed to have those in place. CEO’s inputs and client BC requirements also serve as input for impact analysis.
Defining the plan (Determining BCM strategy)
The next step is to identify the situations that could lead to disruption of the identified critical processes.
The situations could be categorized as:
- Natural and environmental: – Earthquakes, floods, hurricanes etc
- Human related: – Strikes, terrorist attacks, pandemic situation, thefts etc
- IT related: – critical systems failure, virus attacks etc
- Others: – Business Competition, power failure, Client BC contractual requirements
It might not be feasible to have plans for each and every situation, as implementing the defined plans needs to be practically possible. After the situations have been identified one needs to identify different threats, threat severity (how serious will be the impact on business if threat materializes) and their probability of occurrence (likelihood of threat materialization). Based on threat severity and occurrence levels critical risks are identified.
Implementing the plan (Developing and implementing BCP response)
The identified risks and additional client specific BCP requirements serve as inputs to the creation of BCPs. BCPs should focus on mitigation plan for the identified risks. BCP should be comprehensive, detailing roles and responsibilities of all the response teams. Proper budget needs to be allocated. Once the plan is documented the plan should be implemented.
The different implementation as per BCP could include having redundant infrastructure, signing up Service Level Agreements (SLAs) with service providers, having backup power supply, sending backup tapes to offshore sites, and training people in cross skills, having proper medicines or masks for addressing pandemic situations.
BCP should also have proper plans in place to resume business as usual. Business resumption is a critical and very important aspect of business continuity framework.
Testing and improving plan (Exercising, maintaining and reviewing)
Once the plans are documented and implemented the plans should be regularly tested. The tests could be scheduled or as and when the need arises. One can simulate different tests like moving people to other locations, having primary infrastructure down, testing UPS and diesel generator capacity, calling tree tests, evacuation drills, having senior management backups to take decisions, transport arrangements etc.
The tests will help you identify areas which need improvement in the BCP. The gaps between the expected and actual results need to be compared. The test results needs to be published to senior management. The plan needs to be reviewed regularly to update latest threats and have mitigations for the critical ones which will result in continuous lifecycle. One can schedule internal audits or apply for BS25999 certification to ensure proper compliance to BCP requirements.
Pune faces threats of irregular power supply, pandemic out break etc which could lead to business disruptions. One needs to have detailed plans for critical threats to ensure continuity of critical operations. The plans should also have detailed procedure to ensure proper business resumption. Plans may be documented but actual action during emergency situations is very important.
Important note: Contractual requirements
When signing off specific contractual requirements with clients, certain precautions must be taken as follows:
- Before signing stringent SLAs it should be checked that there is a provision for exclusions or relaxations during disaster situations as you will not be able to achieve SLAs during disaster scenarios
- When BCP requirements are defined in client contracts the responsibilities or expectations from the clients should also be clearly documented and agreed to ensure effective execution of the BCP
- BCP requirements can only be effectively implemented when proper budget allocations are planned. So for specific BCP requirements cost negotiations with the client are important. Usually this is ignored, so it is important that the sales team should be appraised before agreeing on BCP requirements with the client.
- Do not sign-off on vague BCP requirements. They should be clear, specific and practically achievable
- Before signing off any contract which has a penalty clause, it should be reviewed thoroughly to ensure that compliance to those clauses is practically possible
About the author: Dipali Inamdar
Dipali Inamdar, Head – IT security in Geometric Ltd, has more than 11 years of experience in Information Technology and Information Security domain. She is a certified CISA, ISO27001 Lead Auditor, BS25999 Lead Auditor and ISO2000 Internal auditor. She has worked in sectors spanning BPO, IT and ITES companies, Finance sector for Information Security and Business Continuity Management. She is currently operating out of Pune and is very passionate about her field. See her linked-in profile for more details.
![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_b.png?x-id=1fb436d3-5146-4d72-a4f6-16959c19ffff)
Immpressive article.
BCP concept is very important in current situation as we recently observed this when Swine Flue pandemic was spreading and everyone was worried to roam around.
Good one…
BCM process should be inbuilt within each process in the organization. There are quite a few discussions / articles on BCM concepts. This one throws light on basic and key concepts…
Good article, appreciate it, the article is clear and straight forward. Good introduction and could be used to create awareness on BC/DR.
Good article, appreciate it, the article throws light on basic and key concepts
Hi Dipali,
Good work.
A very good article with no fillers at all. I personally liked your Important note as it crystalizes certain things that are often missed out. It would be good to see conclusion in your article.
I look forward to reading your article.
Regards,
Parsh
a good note, sums it all in a nutshell. If however, anyone is interested in extensive training on practical approaches to BCP & DRP implementations, please contact us. More details on trainer profile & other service offerings (CISSP, CISA, CISM, SSCP Trainings, Enterprise Systems & Network design and more)listed on http://www.rabcs.com.
Regards,
Rajesh Pandita CISSP CISM CISA, B.E (C.Sc)
MCDBA, MCSA, MCSE+I, MBITT, BNS, BITIL
(ex-CIO Fortune 10 MNC)
(Corporate Information Systems & Security Trainer)
(Enterprise Applications, Systems & Network specialist)
Some additions to the contractual considerations
-Include provisions to utilise clients infratructure during a DR
-Capture in essence what is important during an event
*Data protection
*Uninterrupted Process continuity
*Knowledge retention
I would also note if you are doing business with the Federal government to place close attention to NSPD-51/HSPD-20 in which it clearly defines Federal, state, local, tribal nations and private sector responsibilities to COOP/BCP. If you are under contract with the Federal government providing critical infrastructure support (IT, professional services etc.,) yo have a responsibility to have a viable plan in place. Most RFPs are now requiring BCP from the private sector as a requirement of their response.
Hi Dipali,
In the BCM strategy topic , you havent mentioned anything about the BCM startegies possibly a very high-level over-view which would have been really helpful to teh readers, secondly what i find missing is the important topic Risk assessment which is covered in BCM startegy.
The main concepts are not clearly explained.
Sorry friends ofcourse it is no doubt a good attempt, but quite misguiding.
Regards,
Raj
Immpressive article.
BCP concept is very important in current situation ,i would like to know more about Disaster Recovery
Hi Dipali,
A very good article outlining the basics of Business Continuity. A good start for an introducer.
Regards,
Shailesh.
Raj,
BCP is a very vast topic, this article was basically to make people aware about BCP concepts.
The phases are covered in very brief.
Risk assessment is a very vast topic in First phase.I have briefed about it in the first phase if you read it carefully.
I do not find anything misleading in it, as this a very generic document.
Regards,
Dipali Inamdar
I tend to disagree with Raj. Dipali has done a very good attempt to give a comprehensive overview of Business Continuity Management to a beginner. No doubt Risk Assessment is an important element in BCM which she mention in the plan implementation section. Based on the identified Risks, the mitigation plan should be developed and accordingly implemented. I hope I have clarified the doubts. Best regards
Nalin Wijetilleke MBA,CISA,PMP,CBCP,MBCI
Dipali,
Really a nice article. Very useful for the novice. Looks like an interpretation of BS25999 in plain English. Simple approach but highly effective. Congratulations!
Regards,
Yashodhan
Raj ..
Dipali made an attempt tp provide a basic understanding of BCP /DR …Not for marketting of her classes…Something is better than nothing….
Nice Information…
Thanks a lot madam.. This article will help me a lot in my examination paper..
i have one question to ask :
1) what is basic difference between BCP and DRP??