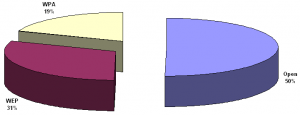
ClubHack, the group hell-bent on hammering some sense of security hygiene into the heads of an ignorant and careless public, went around Pune making a note of how secure or insecure various Wi-Fi hotspots in the city were, and found that a full 50% were not protected at all, and another 31% were only weakly protected. That just leaves 19% adequately protected.
If you have no idea what I am talking about, here is a little bit of explanation. More and more users are now using wireless networking cards to get their internet access. In such a setup, there is a Wi-Fi card that goes into your desktop/laptop (most modern laptops have this built-in), and to complete the connection there is a device that needs to be plugged into your internet connection (i.e. your broadband cable, or telephone line). This device is called an access point (AP), and is typically a wireless router. The computer then communicates wirelessly with your wi-fi router to connect to the internet.
The above report points out that in 50% of all wi-fi access points installed in Pune, there is no protection against random third-party computers from connecting to the AP. That’s like leaving your front door open. Not only can they access the internet using your AP, but more importantly, it is very likely that they can access the other computers on your network, and can tap into the network traffic going back and forth between those computers and the internet. If you are unlucky, they can get access to sensitive data, like passwords to your email account, or worse, bank account. Or, if, like our government, you want to focus on the wrong thing, you can worry that THE TERRORISTS CAN USE YOUR NETWORK TO SEND BOMB THREATS!!! (and we dutifully reported that in PuneTech.)
Of the remaining, 31% think that they have protected their AP using encryption, but the encryption scheme they are using (WEP) is known to be very weak, and can be broken in a matter of minutes. Which means that a hacker (cracker actually) sitting in a car outside your building can easily break into the network without anybody realizing it.
How did ClubHack find out? This is what they did:
On 10th November 2008, ClubHack created a setup in a car which included laptops & GPS enabled devices for the exercise. The car was driven in all the popular areas which included IT parks, multiplexes, residential areas, markets, busy streets etc. While the car was driving at a normal speed, the GPS and wireless enabled devices sensed the availability of wireless signals on the road. These signals were then recorded with details like MAC address of the access point, name of the network, security used, longitude and latitude of the location where the signal of a particular network was highest.
And just in case anybody amongst you is thinking that what they did was illegal and actionable, don’t worry! They took permission of Pune Police to undertake this mission, and Pune Police actually sent an officer to accompany them. For some more details of their project and findings, you can check out the short report, or the full report (PDF).
What should you do? If you are reading PuneTech, then no doubt you are one of the smart ones who are in the 19% that use WPA based encryption. But just in case someone slipped through, what you need to do is educate yourself about wi-fi security issues, and ensure that you change the settings on your wi-fi access point to use one of the WPA based encryption schemes. (There are 6 or 7 variants like WPA-PSK, WPA2-Personal, etc. Any one of them will do.) And please change the default administrator password for your AP. And if you have no clue what I am talking about, get a friend who understands to help you. Or pony up the Rs. 1000 for the wi-fi security workshop that ClubHack is going to conduct next month, or the Rs. 8000 for the wi-fi security training that AirTight networks is going to conduct later this month. This last one is certainly recommended if you are the network admin for one of the IT companies that ClubHack managed to snag during their wardrive.
And just in case the remaining 19% are feeling very pleased with yourself, I should also point out that security guru Bruce Schneier keeps his own wi-fi network open. It is a fascinating, and insightful, and a different take on this issue that you should read. But inspite of Bruce’s sage advice, I keep my router protected with WPA. Because Bruce’s advice amounts to saying that I should leave my door open, but keep all my drawers, and cupboards, and closets and bedroom door locked, and the fridge and TV chained to the wall. I’m not a security guru, and I am sure I’ll leave some door open. Don’t want to take that chance.
Pune company watch: Companies that are doing work related to this area in Pune: Airtight Networks, Symantec, QuickHeal.